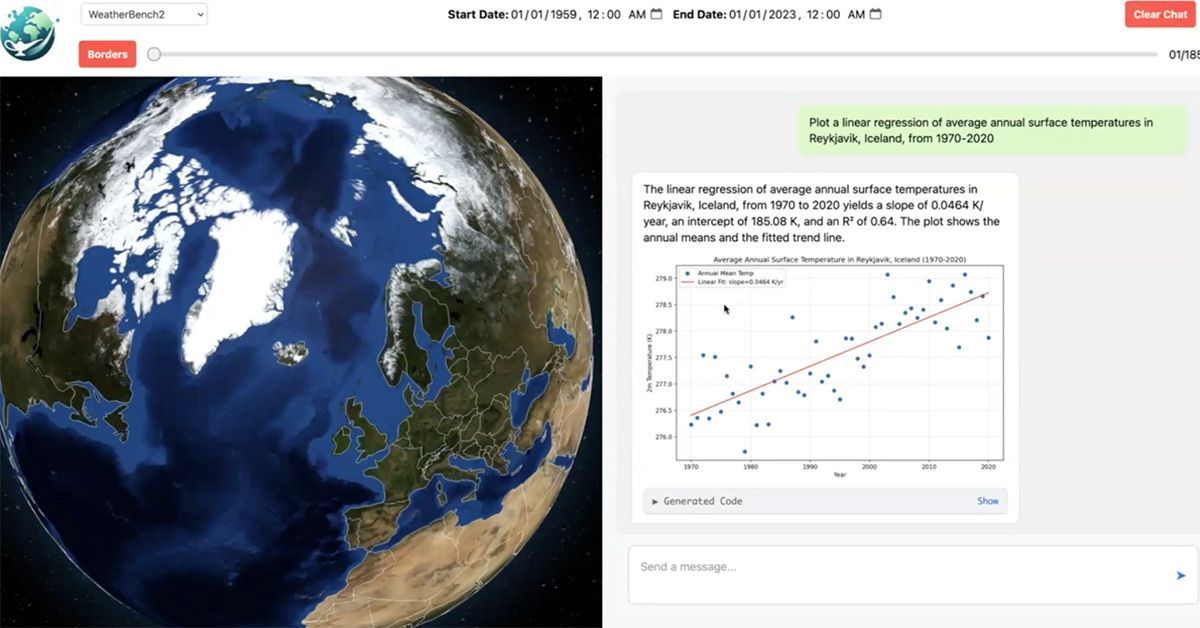
New AI Agent Could Transform How Scientists Study Weather and Climate
A new AI agent could help analyze complex data from weather forecasting models The tool could help democratize earth science Researchers hope to expand the tool to other areas, including climate science Computer scientists and weather scientists have taken the first steps toward creating an AI agent capable of analyzing and answering questions in natural